Configure CloudTrail in AWS
AWS CloudTrail is a web service that records AWS API calls for your account and delivers log files to you.
With CloudTrail, you can get a history of AWS API calls for your account—no matter if you made those calls using the AWS Management Console, AWS Software Development Kits (SDKs), Command Line Interface (CLI) tools, or other AWS services such as AWS CloudFormation.
CloudCheckr can consume CloudTrail logs, which you can leverage for your alerts and reports. However, AWS does not write CloudTrail logs to storage by default; you need to configure it so that CloudCheckr can access and consume it.
Procedure
This procedure will show you how to configure CloudTrail in AWS:
- Log in to the
AWS Management Console.
The AWS services page opens.
- Scroll down to the Management & Governance section and select CloudTrail.
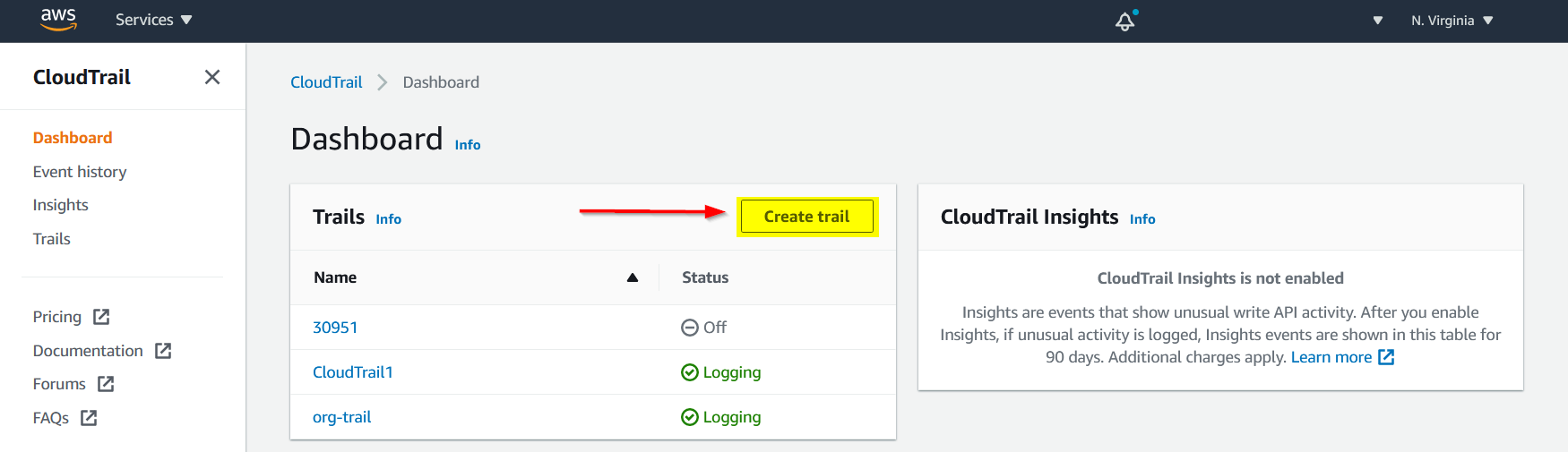
- From the CloudTrail dashboard, click Create trail.
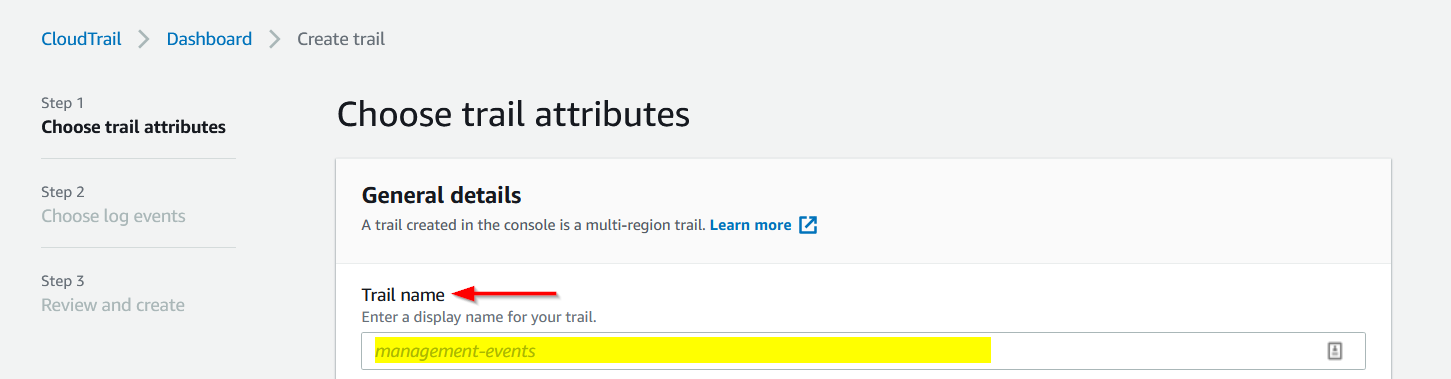
- On the Choose trail attributes page, provide a name for your trail.
- Scroll down to the Storage location section.
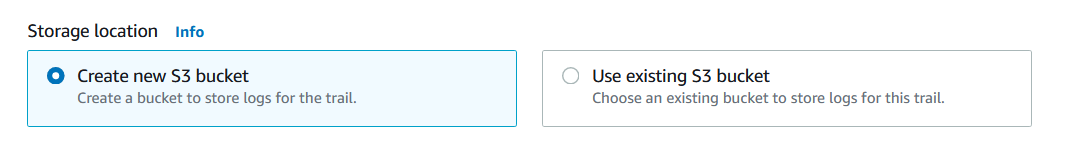
At a minimum, you must record the name of the S3 bucket where you want AWS to write the CloudTrail log.
You must configure an S3 bucket before you can create a cross-account role in CloudFormation or
manually. - For the purposes of this procedure, let's configure an existing S3 bucket:
- Select the Use existing S3 bucket radio button.
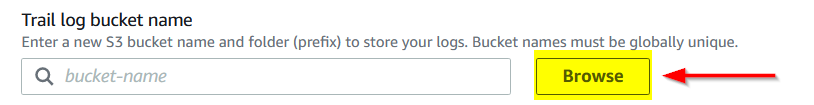
- Click Browse to locate an existing S3 bucket.
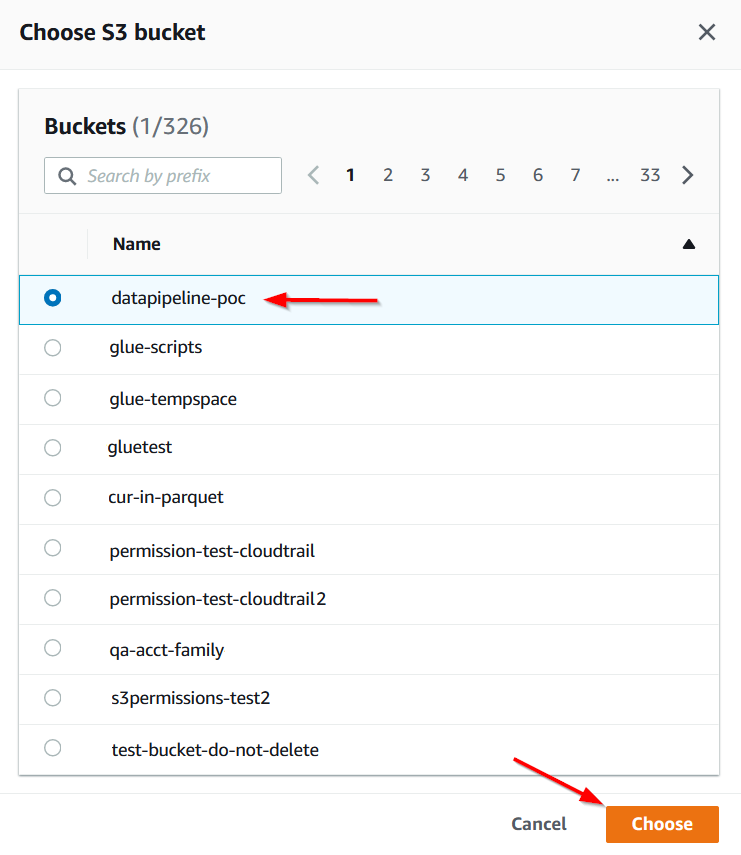
- From the Choose an S3 bucket dialog box, select an S3 bucket from the list and click Choose.
- In the Log file SSE-KMS encryption section, de-select the Enabled checkbox.
- Scroll down to the bottom of the page and click Next.
- On the Choose log events page, leave the default settings, and click Next.
- On the Review and create page, review your settings, and click Next.
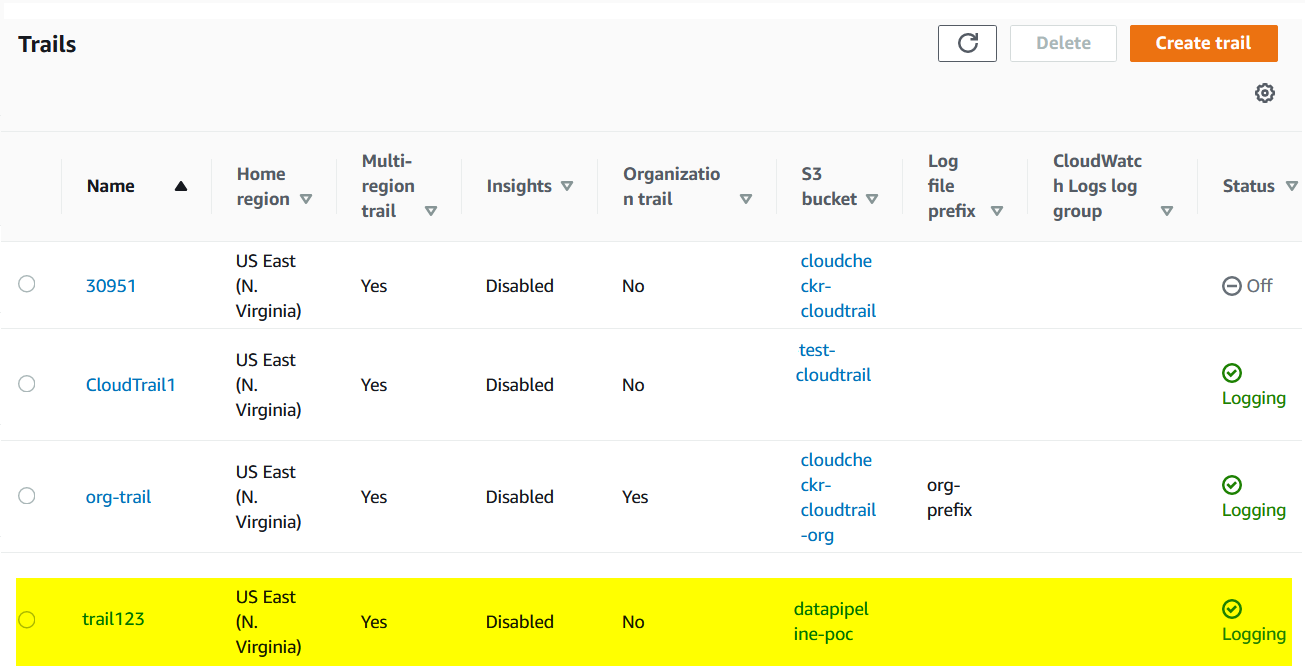
AWS displays your new CloudTrail in the list: