Best Practice Report
Cloud computing providers present a large, robust offering with a seemingly infinite number of configuration options to tailor your deployment perfectly around your needs. However, the flexibility and sheer number of choices that a cloud provider offers when setting up your services are both a blessing and a curse. It can be easy to overlook security loopholes, deploy options that aren't the most cost-effective, or miss beneficial features that are hidden within the API.
Categories
Our application takes a detailed look at your deployment to ensure your infrastructure is configured properly, and highlight areas that may be cause for concern. These checks will focus on four key areas: security, availability, cost, and usage.
Security
While your cloud computing provider handles security of their data center, users are responsible for network, host, and application-level security. CloudCheckr will look and see if you are setting proper permissions, if security groups are being utilized properly, if access and permission controls are configured correctly, if proper password policies are in place, if resources are accessible by the public internet, and several other items.
Availability
When items are launched in your deployment, it's important that they are accessible. However, sometimes things can go wrong, such as instances becoming unhealthy or certain data centers becoming unreachable. CloudCheckr will look at your deployment to not only verify that everything is up and running, but also ensure that your architecture is properly configured to respond when things do go awry.
Cost
When launching and maintaining an infrastructure, it's easy to lose track of what's out there and what's no longer needed. CloudCheckr can help with this. We will look for items that exists but aren't being used, and highlight those for you. Cost checks will also show you potential cost savings by making RI purchases, optimizing your subscriptions, or leveraging any available discounts, as well as migrating resources to current generation offering types.
Usage
There are many options within a cloud environment that, though highly recommended, may not be consistently or properly deployed. CloudCheckr will review your architecture to see whether you are taking advantage of these features, and whether they are being used in the most advantageous way. We will ensure that autoscaling is configured, and configured properly, within your servers. We'll ensure that the users in your identity management portals are created according to best practices. That backups are taken automatically and retained for an appropriate amount of time. And that resources are being properly utilized.
Trusted Advisor
If customers use AWS Trusted Advisor and have provided CloudCheckr with access to this feature, the application can import the results into the AWS Trusted Advisor tab in the report. 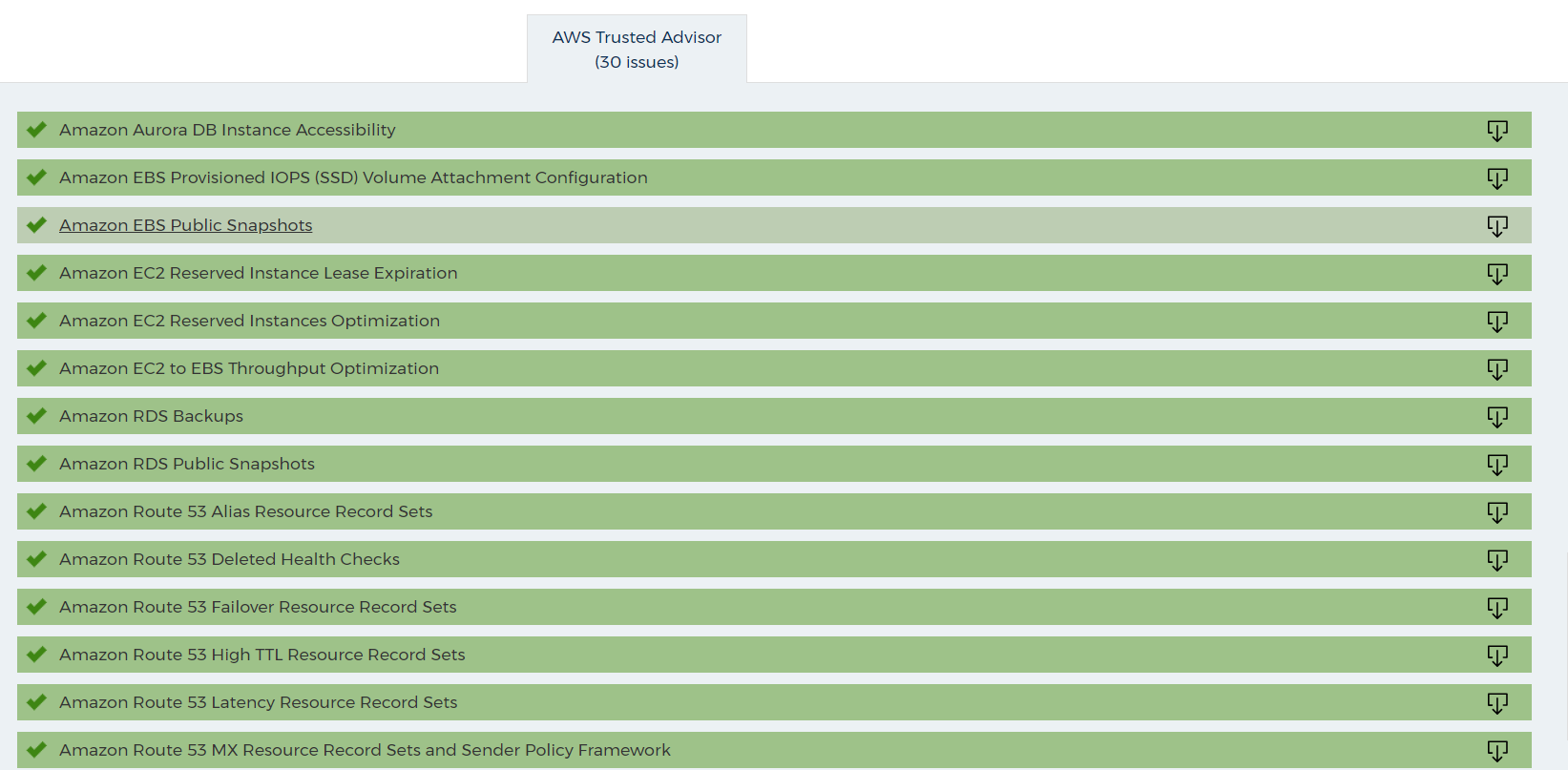
Azure Advisor & Azure Security Center
Users who also utilize Azure Advisor can have their Azure Advisor results automatically imported into their CloudCheckr Best Practice report. The functionality of the Azure Advisor checks work the same as native CloudCheckr best practice checks. Click on any item within the Azure Advisor tab to expand and view further details. These checks are also categorized into importance categories, with green meaning no issues were reported by Azure Advisor.
Filters
The top section of the report allows you to filter your checks by:
- Category
- Importance
- Tag
- Ignored Checks
- History
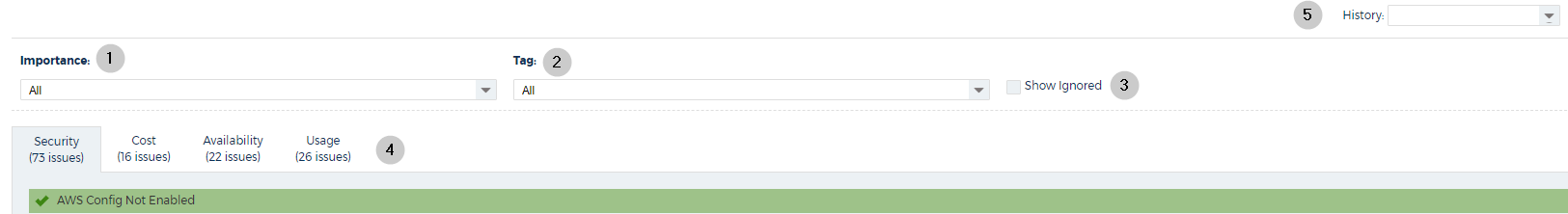
The table references each callout in the screenshot.
Callout |
Name |
To Filter: |
1 |
Importance |
Select All, High, Medium, Low, Informational , or Ok from the Importance drop-down menu. |
2 |
Tag |
Select a resource tag associated with your account from the Tag drop-down menu. |
3 |
Show Ignored |
Select or deselect the Show Ignored check box to view or restore those items that you have flagged to ignore. |
4 |
Tab |
Click one of the report tabs: Availability, Cost, Security, Usage, or Trusted Advisor |
5 |
History |
Select a day from the History drop-down menu and filter for the specific date. |
After you have made your selections, click Filter to apply your changes to the report.
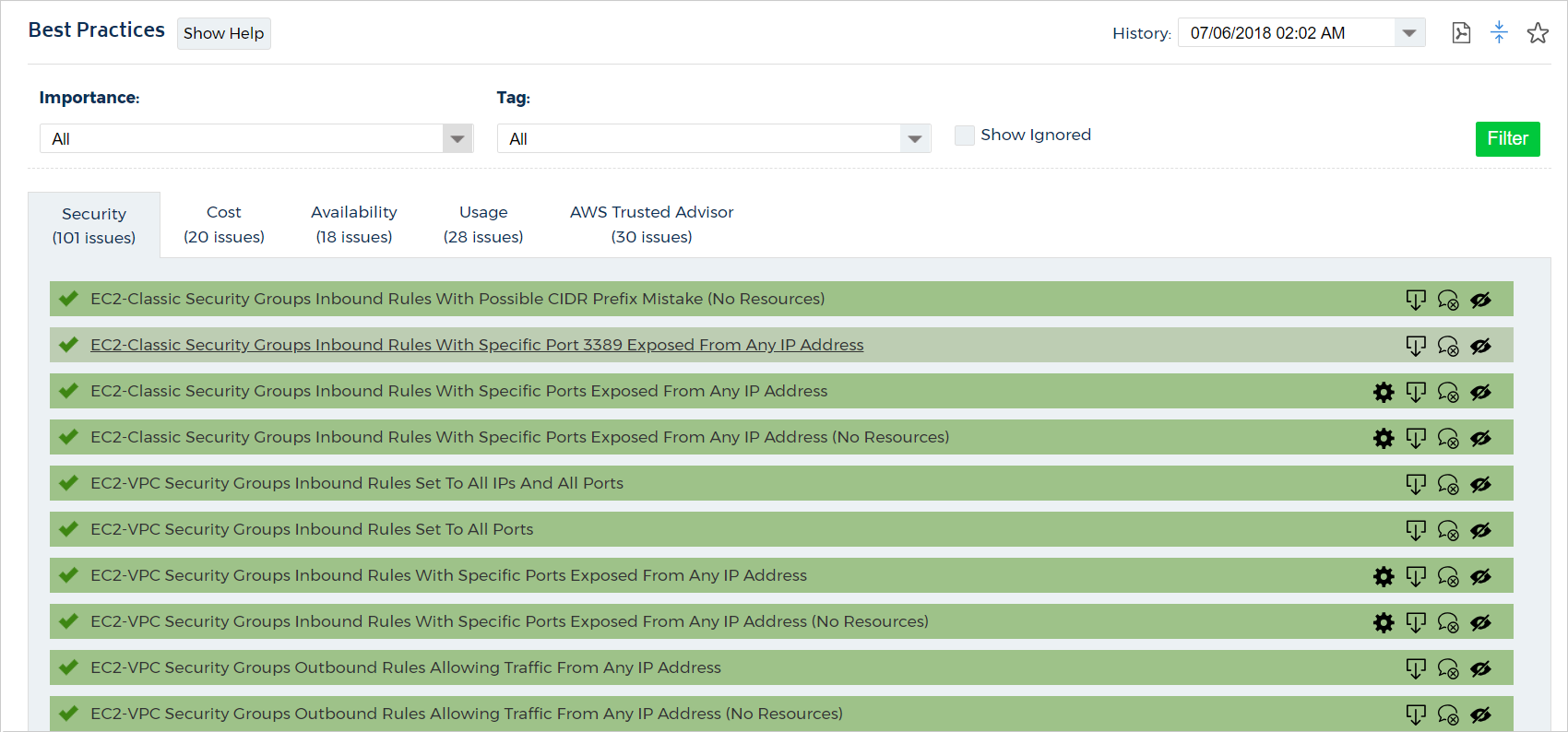
Icons
The items in the report are also categorized by icons and colors.
Color |
Icon |
Description |
Example |
Red |
 |
High |
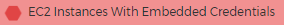 |
Orange |
Medium |
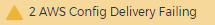 |
|
Yellow |
 |
Low |
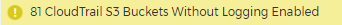 |
Blue |
 |
Informational |
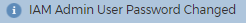 |
Green |
 |
No issues found |
 |
Best Practice Check Details
The report lists the name of each best practice check and the number of items that CloudCheckr identified which meet the criteria for the best practice check.
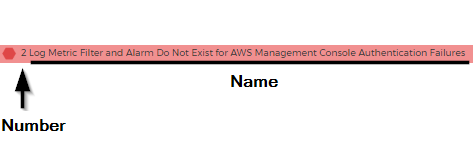
If only one item meets the criteria for the best practice check, no number will be displayed.
If no items meet the criteria for the best practice check and the check passes, the bpc will be displayed in green with a checkmark.
To view the details for a Best Practice Check, click the name.
The Best Practice Check expands and identifies the items in your deployment that met the requirements for the selected best practice check.
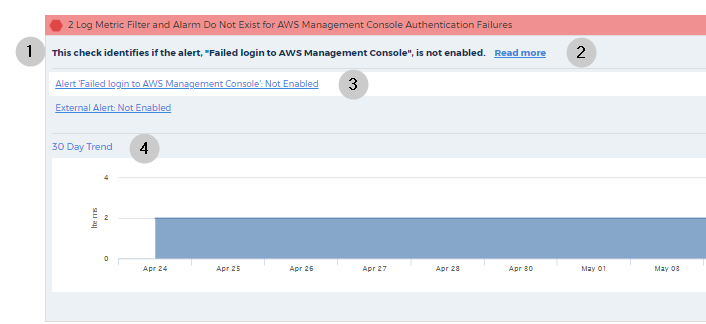
The table references each callout in the screenshot.
Callout |
Name |
Description |
1 |
Summary |
Describes what the BPC looked for in your deployment. |
2 |
Read More |
Contains more detail about the check results. See Read More section for more information. |
3 |
Link |
Redirects you to the details report for the selected item. A View All... link redirects you to the details report for all items. |
4 |
30-Day Trend Graph |
Shows how many items were found for a specific check each day within the last 30 days. If you see any spikes or anomalies that you want to investigate, select a date from the History drop-down menu to filter the report by the selected date. |
Read More
When you click Read More, you will see the following details:
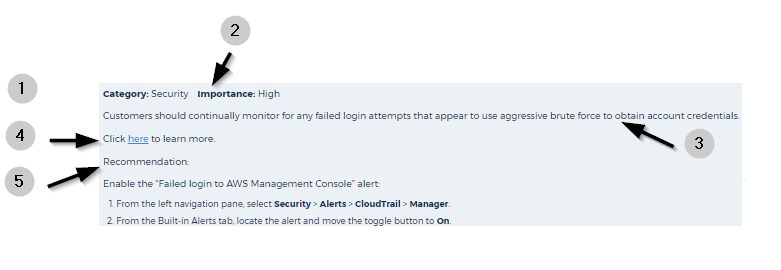
The table references each callout in the screenshot.
Callout |
Name |
Description |
1 |
Category |
Describes the type of best practice check: availability, cost, security, or usage. |
2 |
Importance |
Identifies the level of importance: high, medium, low, or informational. |
3 |
Description |
Provides an overview of the feature that the best practice check was run against, why the check is important, and how it impacts an account. |
4 |
Link |
Links to the relevant AWS documentation. |
5 |
Recommendation/Remediation |
Tells you how to prevent a potential adverse condition or how to fix a current adverse condition. |
Manage Best Practice Checks
To the right of each check, you will find several icons. The number and type of icons depends on the selected check.
The table identifies each icon and the action(s) that you can perform with it.
Icon |
Name/Tooltip |
Purpose |
 |
Export |
Export details of the selected check to comma-separated value (CSV) file. |
 |
Notifications |
Create email notifications that selected users will receive when new issues are discovered or configure to have emails sent daily regardless of any changes. See the Configure Best Practice Check Notification topic for more information. |
 |
Notify of New Issues |
Send email notifications to selected users will receive when new issues with an ignored check are discovered. |
 |
Ignore Check |
Hides checks that are irrelevant to your deployment. Also, the application will not send include Ignored checks in any email notifications. |
 |
Restore Check |
Restores the check that you had selected to ignore. |
 |
Edit Ignore Reason |
Modify the reason why you are ignoring a check. |
 |
Configure |
Modify the parameters that trigger a check. For example, you can dictate the CPU Utilization % and Time Period that determines when an EC2 instance will be considered idle. |
 |
Tags |
Configure the check to only report on resources that have specific resource tags. After configuring this option, you must run a new report update for this change to take effect. |
If you ignore an item, as opposed to a check, the check will still show up in your report and email, but the individual item(s) you have ignored will be hidden.
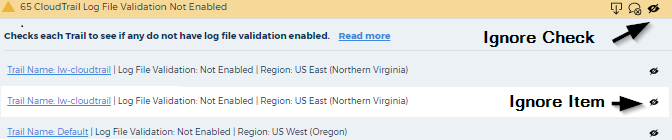
This functionality is also available on the individual items found within each check. If you expand a check, you can click the Hide  icon to the right of the item to ignore that specific item while leaving the main best practice check active.
icon to the right of the item to ignore that specific item while leaving the main best practice check active.